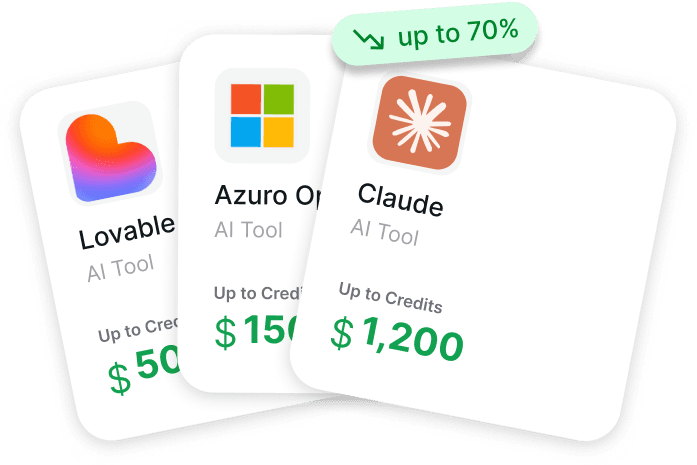
AI Perks curates and provides access to exclusive discounts, credits, and deals on AI tools, cloud services, and APIs to help startups and developers save money.
OpenClaw's Security Crisis - The Biggest AI Agent Scandal of 2026
OpenClaw - the open-source AI agent with 180,000+ GitHub stars - has been hit by the worst security crisis in AI tool history. In February 2026, researchers discovered 7 critical vulnerabilities, 135,000+ exposed instances, and 800+ malicious skills delivering malware through the official ClawHub marketplace.
Google began banning paying AI subscribers who use OpenClaw. Meta prohibited it on all work devices. CrowdStrike, Cisco, and Nature published urgent advisories.
If you run OpenClaw, the first thing to do is secure legitimate API credentials through AI Perks - leaked and stolen keys from compromised instances are already circulating online.
Top AI Credits for Startups
Apply directly through these verified programs.
Claude $10,000 credits
Eligible for early-stage startups
OpenAI $2,500 credits
Eligible for early-stage startups
Anthropic $25,000 credits
Eligible for early-stage startups
AWS $300,000 credits
Eligible for early-stage startups
Google Cloud $350,000 credits
Eligible for early-stage startups
Lovable $6,000 credits
Eligible for early-stage startups
Crisis Timeline - How It All Unfolded
The crisis didn't happen overnight. It escalated across a three-week window as security researchers peeled back layer after layer of vulnerabilities.
| Date | Event |
|---|---|
| Jan 29 | CVE-2026-25253 silently patched in OpenClaw v2026.1.29 |
| Feb 3 | CVE-2026-25253 publicly disclosed - CVSS 8.8 (one-click RCE) |
| Feb 4 | Additional command injection CVE disclosed |
| Feb 5 | Researchers discover 341 malicious skills on ClawHub (~12% of registry) |
| Feb 6 | Moltbook breach exposes 1.5 million API tokens |
| Feb 7-8 | Google begins restricting AI subscribers using OpenClaw |
| Feb 9 | SecurityScorecard reports 40,000+ exposed OpenClaw instances |
| Feb 15 | Exposed instances grow to 135,000+; malicious skills rise to 800+ |
| Feb 17 | Cline CLI 2.3.0 supply chain attack stealthily installs OpenClaw |
| Feb 20 | Meta bans OpenClaw on work devices; The Register publishes full Cline report |
Three weeks. That's how fast OpenClaw went from the most exciting open-source project in history to the biggest security cautionary tale in AI.
The 7 Vulnerabilities That Shook OpenClaw
Seven CVEs were disclosed within weeks of each other. Three have public exploit code available, meaning anyone can use them against unpatched instances.
CVE-2026-25253 - One-Click Remote Code Execution (CVSS 8.8)
This was the big one. A malicious link sent through any messaging platform - WhatsApp, Telegram, Discord - could hijack an entire OpenClaw instance in milliseconds.
The vulnerability exploited the gatewayURL query parameter to exfiltrate authentication tokens. Once an attacker had the token, they could execute arbitrary commands on the victim's machine. Full system access with one click.
The fix was released in v2026.1.29 on January 29, but the CVE wasn't publicly disclosed until February 3. Researchers estimate thousands of instances remained unpatched for weeks.
The Other Six CVEs
| Vulnerability | Type | Severity | Impact |
|---|---|---|---|
| SSRF (Server-Side Request Forgery) | Network | High | Attackers access internal services through OpenClaw |
| Missing Authentication | Access Control | Critical | No credentials required to control exposed instances |
| Path Traversal | File System | High | Read or write arbitrary files on the host machine |
| Command Injection | Execution | High | Execute system commands through crafted inputs |
| Token Exfiltration (Gateway) | Authentication | Critical | Steal session tokens via malicious URLs |
| Insecure Default Configuration | Configuration | Medium | Binds to 0.0.0.0:18789 - listens on all network interfaces |
The default configuration issue deserves special attention. Out of the box, OpenClaw listens on all network interfaces on port 18789 with no authentication required. This means any newly installed instance is immediately accessible to anyone on the same network - or the entire internet if the port is exposed.
Top AI Credits for Startups
Apply directly through these verified programs.
Claude $10,000 credits
Eligible for early-stage startups
OpenAI $2,500 credits
Eligible for early-stage startups
Anthropic $25,000 credits
Eligible for early-stage startups
AWS $300,000 credits
Eligible for early-stage startups
Google Cloud $350,000 credits
Eligible for early-stage startups
Lovable $6,000 credits
Eligible for early-stage startups
135,000 Exposed Instances - The Scale of the Problem
SecurityScorecard's STRIKE team conducted an internet-wide scan and found the numbers were staggering.
Key findings:
- 135,000+ OpenClaw instances exposed to the public internet
- 93.4% of exposed instances exhibited authentication bypass conditions
- 5,194 instances actively verified as vulnerable to known CVEs
- 53,000+ instances linked to IP addresses associated with known threat actors
The numbers grew fast. An earlier independent study on February 9 found 42,665 exposed instances. Six days later, the count had more than tripled.
What does "exposed" mean? It means the OpenClaw instance is reachable from the internet with no authentication. Anyone who finds it can send commands, read data, access connected messaging accounts, and execute code on the host machine.
For users running OpenClaw with legitimate API credentials from AI Perks - check immediately whether your instance is publicly accessible. If it is, shut it down, rotate your API keys, and enable authentication before reconnecting.
800+ Malicious Skills - The ClawHub Supply Chain Attack
ClawHub is OpenClaw's official skill marketplace - the equivalent of npm for Node.js or pip for Python. It had roughly 3,000+ skills when the crisis began.
Researchers found 20% of them were malicious.
The initial scan on February 5 discovered 341 malicious skills across the registry. A follow-up scan on February 15 found the number had grown to 800+ - meaning roughly one in five ClawHub skills was designed to steal user data.
What the Malicious Skills Do
The primary payload was Atomic macOS Stealer (AMOS) - a well-known credential-stealing malware that targets:
- Browser passwords and cookies (Chrome, Firefox, Safari, Brave)
- Cryptocurrency wallets (MetaMask, Phantom, Coinbase Wallet)
- Keychain passwords on macOS
- System credentials and SSH keys
Users who installed any unverified ClawHub skill during this period should assume their credentials are compromised.
The Cline CLI Supply Chain Attack (February 17)
On February 17, security researchers discovered that Cline CLI version 2.3.0 - a popular command-line tool - had been compromised to silently install OpenClaw on users' machines. The malicious version was live for approximately 8 hours before being discovered and pulled.
An estimated 4,000 downloads occurred during the window. Users who installed Cline CLI during this period may have an OpenClaw instance running without their knowledge.
Top AI Credits for Startups
Apply directly through these verified programs.
Claude $10,000 credits
Eligible for early-stage startups
OpenAI $2,500 credits
Eligible for early-stage startups
Anthropic $25,000 credits
Eligible for early-stage startups
AWS $300,000 credits
Eligible for early-stage startups
Google Cloud $350,000 credits
Eligible for early-stage startups
Lovable $6,000 credits
Eligible for early-stage startups
Google and Meta Ban OpenClaw - Industry Response
The security crisis triggered corporate backlash from the biggest names in tech.
Google began mass-restricting paying Gemini AI Pro and Ultra subscribers ($249/month plans) who used OpenClaw to access models. Users reported being banned without warning, losing access to services they were paying for. Google's position: using third-party tools to access AI models violates terms of service.
Meta issued an internal directive prohibiting OpenClaw on all work devices. Employees were warned that using OpenClaw could result in termination. Multiple other tech firms followed suit, according to reports from Korea Times.
CrowdStrike published a detailed advisory calling OpenClaw "a new class of security risk - an autonomous agent with broad system access that most users deploy without basic security hygiene."
Cisco described personal AI agents like OpenClaw as "a security nightmare" in a blog post from their security team.
Nature published an article titled "OpenClaw AI chatbots are running amok - these scientists are listening in," documenting the academic community's growing concern.
The message from industry was clear: OpenClaw is powerful, but the default security posture is unacceptable for professional use.
How to Protect Yourself If You Run OpenClaw
The crisis is serious, but OpenClaw is still usable with proper precautions. Here are the essential steps, starting with the most important.
Step 1: Get Legitimate API Credits
Never use leaked, shared, or "free" API keys from the internet. The Moltbook breach exposed 1.5 million API tokens. Stolen keys are circulating on dark web forums and Telegram channels.
Get your own legitimate credits through AI Perks:
| Credit Program | Available Credits | How to Get |
|---|---|---|
| Anthropic Claude (Direct) | $1,000 - $25,000 | AI Perks Guide |
| OpenAI (GPT-4) | $500 - $50,000 | AI Perks Guide |
| AWS Activate (Bedrock) | $1,000 - $100,000 | AI Perks Guide |
| Microsoft Founders Hub | $500 - $1,000 | AI Perks Guide |
Total potential: $3,000 - $176,000 in legitimate credits
With your own keys from AI Perks, you control what's exposed. If a breach happens, you can rotate your keys immediately without depending on compromised infrastructure.
Step 2: Update to v2026.2.22 Immediately
The latest release includes 40+ security hardening fixes, gateway authentication, and device management. Check your version and update:
openclaw --version
openclaw update
Any version before 2026.1.29 is vulnerable to one-click RCE. Any version before 2026.2.22 is missing critical security hardening.
Step 3: Enable Authentication
OpenClaw ships with authentication disabled by default. This is the single biggest reason 93.4% of exposed instances had auth bypass.
Enable it in your configuration:
security:
authentication: true
gateway_auth: true
Step 4: Audit Your Installed Skills
Remove any ClawHub skill you didn't personally verify. With 20% of the registry compromised, the safest approach is to uninstall everything and only reinstall skills you've reviewed:
openclaw skill list
openclaw skill inspect [skill-name]
openclaw skill remove [suspicious-skill]
Step 5: Follow the Full Hardening Guide
For a complete 10-step security checklist covering network restrictions, sandbox configuration, logging, and spending limits - read our OpenClaw Security Guide.
Top AI Credits for Startups
Apply directly through these verified programs.
Claude $10,000 credits
Eligible for early-stage startups
OpenAI $2,500 credits
Eligible for early-stage startups
Anthropic $25,000 credits
Eligible for early-stage startups
AWS $300,000 credits
Eligible for early-stage startups
Google Cloud $350,000 credits
Eligible for early-stage startups
Lovable $6,000 credits
Eligible for early-stage startups
Safer Alternatives Worth Considering
If the security crisis has you reconsidering OpenClaw, there are managed alternatives that handle security for you. The trade-off: less customization, but no CVEs to worry about.
| Feature | OpenClaw (Self-Hosted) | Claude Code | Manus AI | ChatGPT Agent |
|---|---|---|---|---|
| Security Model | You manage everything | Anthropic-managed | Meta-managed | OpenAI-managed |
| CVE History | 7 CVEs in Feb 2026 | None public | None public | None public |
| Data Location | Your device | Cloud | Cloud sandbox | Cloud |
| Customization | Full control | Code-focused | Task-focused | General purpose |
| Cost | API credits only | $20-$200/month | $39-$199/month | $20-$200/month |
Every alternative still requires AI API credits to run at full capacity. AI Perks covers credit programs for Anthropic, OpenAI, AWS, Google Cloud, and more - so you're covered regardless of which tool you choose.
For a detailed breakdown of each alternative, see our Best OpenClaw Alternatives guide.
Frequently Asked Questions
Was OpenClaw hacked in February 2026?
OpenClaw itself wasn't hacked in the traditional sense. Seven critical vulnerabilities were discovered and disclosed, 135,000+ instances were found exposed to the internet without authentication, and 800+ malicious skills were found on ClawHub delivering credential-stealing malware. The Moltbook breach also exposed 1.5 million API tokens.
Is OpenClaw safe to use right now?
Yes, with proper configuration. Update to v2026.2.22, enable authentication, audit your skills, and use legitimate API credentials from AI Perks. An unhardened default installation is not safe - but a properly configured instance with the latest patches addresses all known vulnerabilities.
Why did Google ban OpenClaw users?
Google restricted paying Gemini AI subscribers who used OpenClaw to access Google's AI models through third-party tools. This violates Google's terms of service. Users reported losing access to $249/month plans without warning. Use direct API credits from AI Perks instead of consumer subscriptions.
What is the Cline CLI supply chain attack?
On February 17, 2026, Cline CLI version 2.3.0 was compromised to silently install OpenClaw on users' machines. The malicious version was live for approximately 8 hours before being pulled. An estimated 4,000 downloads occurred. If you installed Cline CLI during this window, check for unauthorized OpenClaw installations.
How many malicious OpenClaw skills exist on ClawHub?
As of mid-February 2026, researchers found 800+ malicious skills on ClawHub - roughly 20% of the entire registry. The primary payload is Atomic macOS Stealer (AMOS), which targets browser passwords, cryptocurrency wallets, and system credentials. Only install skills you've personally reviewed.
What should I do if my OpenClaw instance was exposed?
Immediately: shut down the instance, rotate all API keys, change passwords for any connected accounts (email, messaging platforms, crypto wallets), and scan for malware. Then update to v2026.2.22, enable authentication, and get fresh legitimate API credits from AI Perks before reconnecting.
Is OpenClaw still worth using after the security crisis?
OpenClaw remains the most powerful open-source AI agent available. The security issues stem from insecure defaults and a rapidly growing skill ecosystem - not fundamental design flaws. With proper hardening, legitimate credentials, and careful skill management, it's still a compelling tool. The key lesson: never run it with default settings.
Top AI Credits for Startups
Apply directly through these verified programs.
Claude $10,000 credits
Eligible for early-stage startups
OpenAI $2,500 credits
Eligible for early-stage startups
Anthropic $25,000 credits
Eligible for early-stage startups
AWS $300,000 credits
Eligible for early-stage startups
Google Cloud $350,000 credits
Eligible for early-stage startups
Lovable $6,000 credits
Eligible for early-stage startups
The Security Crisis Is a Wake-Up Call for AI Agents
OpenClaw's crisis exposed a hard truth: open-source AI agents with system-level access require serious security hygiene. The default "install and go" experience that made OpenClaw viral is the same thing that left 135,000+ instances exposed.
The OpenClaw Foundation (now backed by OpenAI after Peter Steinberger's move) is actively fixing these issues. Version 2026.2.22 includes 40+ security hardening patches. The community is stronger for having gone through this.
But the responsibility still falls on you. Update your installation, enable authentication, audit your skills, and start with legitimate API credentials from AI Perks. Whether you stick with OpenClaw or switch to a managed alternative - you need real credits, not stolen keys.
Don't let a security crisis cost you more than it has to. Get legitimate AI credits and run your tools safely at getaiperks.com.